Captive networks are also called 'subscription'or 'Wi-Fi Hotspot' networks. You can find these networks in coffee shops, Internet cafes, hotels, airports, and other public locations. In some countries and regions, wireless carriers sponsor and maintain captive networks.
Join a captive Wi-Fi network
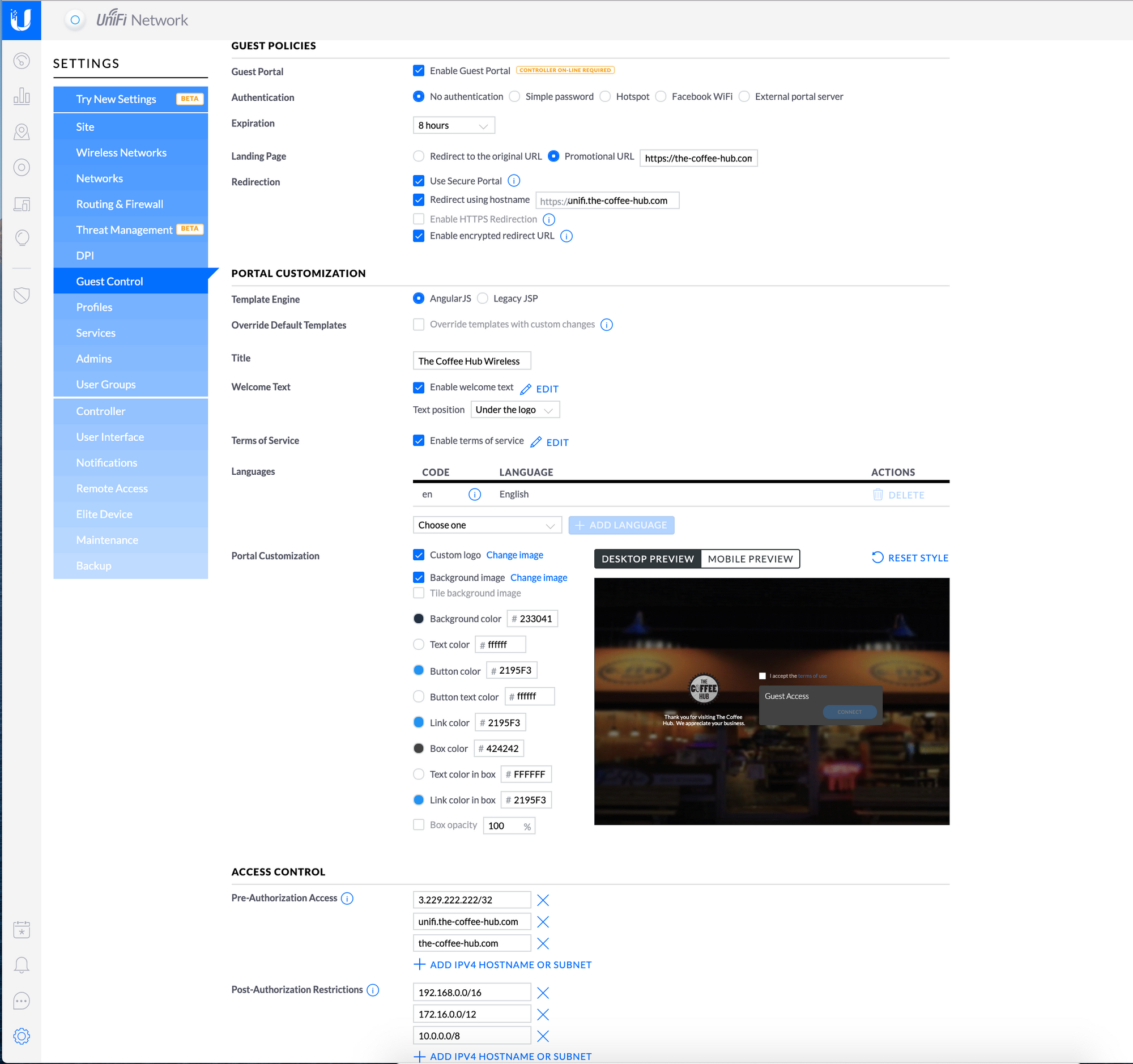
- A captive portal facilitates direct audience engagement at a critical point during a user’s Internet experience, and is therefore a powerful medium that can be used for a flexible range of use cases. Example captive portal page Cisco Meraki’s cloud management platform includes built-in captive portal functionality with.
- This is a bug in macOS Catalina (still present with the latest patchlevel, i.e. 10.15 with the supplemental update from 15th October 2019). For some reason the Captive Portal Assistant (the app that produces the captive portal popup window whenever you connect to a WiFi hotspot) won't start automatically.
To join a captive Wi-Fi network:

Feb 07, 2019 MAC Address Control¶ The MACs tab defines actions for MAC addresses that can be either passed through the portal for this zone without requiring authentication, or blocked from reaching the portal. To manage these MAC entries: Navigate to Services Captive Portal. Click on the line for the Zone to edit. Click the MACs tab. Click Add to add a.
- Tap Settings > Wi-Fi.
- Tap the name of the network, then wait for a login screen to appear. Or tap next to the network's name, then tap Join Network.
- If prompted, enter a user name and password, enter an email address, or acknowledge terms and conditions.
After you log in, you should be able to access the Internet. Fees and other charges might apply when you use captive Wi-Fi networks. Contact the network provider for more information.
If you cancel before you log in to the network
When you tap Cancel on the login screen, you disassociate the device from the captive Wi-Fi network.
If you joined the network from the Wi-Fi screen by tapping the button, a message says that the network isn't connected to the Internet. You can choose one of these options:
- Without Internet dismisses the Welcome screen and turns off Auto-Login for the network. It keeps your device associated with the network and allows you to use the network in other ways.
- Other Network dismisses the Welcome screen and disassociates your device from the network. It returns you to the Wi-Fi Settings screen where you can choose a different network.
- Cancel returns you to the Welcome screen.
Join Wi-Fi networks automatically

Your iPhone, iPad, and iPod touch can remember network and login information so that you can automatically reconnect to that network when you're in range.
If your device doesn't automatically join a captive Wi-Fi network, follow these steps:
- Tap Settings > Wi-Fi.
- Tap next to the network name.
- Make sure that Auto-Join is on.
If you don't want to connect automatically, turn off Auto-Join. To see the Welcome screen the next time that you connect to the network, turn off Auto-Login.
Authentication is a process of identifying a user by through a valid username and password or based on their MAC addresses. The following authentication methods are supported in Instant:
| | 802.1X authentication |
| | MAC authentication |
| | MAC authentication with 802.1X authentication |
| | Captive Portal Authentication |
| | MAC authentication with Captive Portal authentication |
| | 802.1X authentication with Captive Portal Role |
| | WISPr authentication |
802.1X authentication
802.1X is an IEEE standard that provides an authentication framework for WLANs. 802.1x uses the Extensible Authentication Protocol (EAP) to exchange messages during the authentication process. The authentication protocols that operate inside the 802.1X framework include EAP-Transport Layer Security (EAP-TLS), Protected EAP (PEAP), and EAP-Tunneled TLS (EAP-TTLS). These protocols allow the network to authenticate the client while also allowing the client to authenticate the network. For more information on EAP authentication framework supported by the IAP, see Supported EAP Authentication Frameworks.
802.1X authentication method allows a
For more information on configuring a
MAC authentication
MAC authentication is used for authenticating devices based on their physical MAC addresses. MAC authentication requires that the MAC address of a machine matches a manually defined list of addresses. This authentication method is not recommended for scalable networks and the networks that require stringent security settings. For more information on configuring a
Captive Portal For Apple Device
MAC authentication with 802.1X authentication
This authentication method has the following features:
| | MAC authentication precedes 802.1X authentication - The administrators can enable MAC authentication for 802.1X authentication. MAC authentication shares all the authentication server configurations with 802.1X authentication. If a wireless or wired client connects to the network, MAC authentication is performed first. If MAC authentication fails, 802.1X authentication does not trigger. If MAC authentication is successful, 802.1X authentication is attempted. If 802.1X authentication is successful, the client is assigned an 802.1X authentication role. If 802.1X authentication fails, the client is assigned a deny-all role or mac-auth-only role. |
| | MAC authentication only role - Allows you to create a mac-auth-only role to allow role-based access rules when MAC authentication is enabled for 802.1X authentication. The mac-auth-only role is assigned to a client when the MAC authentication is successful and 802.1X authentication fails. If 802.1X authentication is successful, the mac-auth-only role is overwritten by the final role. The mac-auth-only role is primarily used for wired clients. |
| | L2 authentication fall-through - Allows you to enable the l2-authentication-fallthrough mode. When this option is enabled, the 802.1X authentication is allowed even if the MAC authentication fails. If this option is disabled, 802.1X authentication is not allowed. The l2-authentication-fallthrough mode is disabled by default. |
For more information on configuring a
Captive Portal Authentication
Captive portal authentication is used for authenticating guest users. For more information on Captive Portal authentication, see Captive Portal for Guest Access.
Captive Portal Mac Os Catalina
MAC authentication with Captive Portal authentication
Portal For Mac Torrent
This authentication method has the following features:
| | If the captive portal splash page type is Internal-Authenticated or External-RADIUS Server, MAC authentication reuses the server configurations. |
| | If the captive portal splash page type is Internal-Acknowledged or External-Authentication Text and MAC authentication is enabled, a server configuration page is displayed. |
| | If the captive portal splash page type is none, MAC authentication is disabled. |
| | You can configure the mac-auth-only role when MAC authentication is enabled with captive portal authentication. |
For more information configuring a
802.1X authentication with Captive Portal Role
This authentication mechanism allows you to configure different captive portal settings for clients on the same SSID. For example, you can configure an 802.1x SSID and create a role for captive portal access, so that some of the clients using the SSID derive the captive portal role. You can configure rules to indicate access to external or internal captive portal, or none. For more information on configuring captive portal roles for an SSID with 802.1x authentication, see Configuring Captive Portal Roles for an SSID.
WISPr authentication

Wireless Internet Service Provider roaming (WISPr) authentication allows a smart client to authenticate on the network when they roam between wireless Internet service providers, even if the wireless hotspot uses an Internet Service Provider (ISP) with whom the client may not have an account.
If a hotspot is configured to use WISPr authentication in a specific ISP and a client attempts to access the Internet at that hotspot, the WISPr AAA server configured for the ISP authenticates the client directly and allows the client to access the network. If the client only has an account with a partner ISP, the WISPr AAA server forwards the client’s credentials to the partner ISP’s WISPr AAA server for authentication. When the client is authenticated on the partner ISP, it is also authenticated on your hotspot’s own ISP as per their service agreements. The IAP assigns the default WISPr user role to the client when your ISP sends an authentication message to the IAP. For more information on WISPr authentication, see Configuring WISPr Authentication.
